Cybercriminals laundered $8.6 billion worth of cryptocurrency in 2021 – Chainalysis report

Overall, cybercriminals have laundered over $33 billion worth of cryptocurrency since 2017, with most of the total over time moving to centralized exchanges.
Going by the amount of cryptocurrency sent from illicit addresses to addresses hosted by services, cybercriminals laundered $8.6 billion worth of cryptocurrency in 2021, according to a Chainalysis – 2022 Crypto Crime Report.
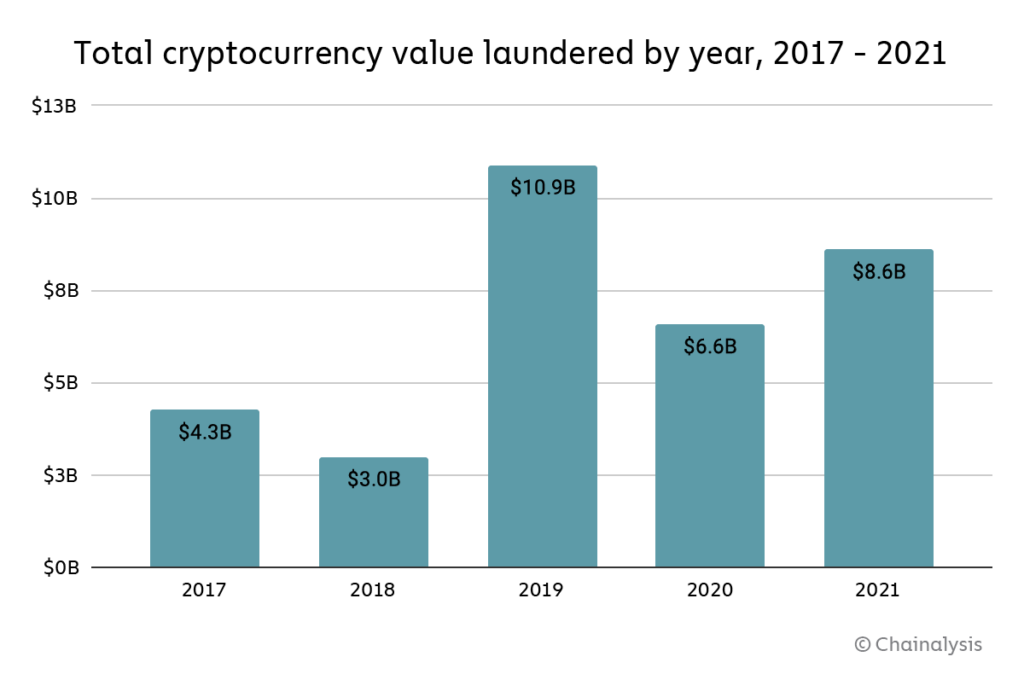
That represents a 30% increase in money laundering activity over 2020, though such an increase is unsurprising given the significant growth of both legitimate and illicit cryptocurrency activity in 2021. We also need to note that these numbers only account for funds derived from “cryptocurrency-native” crime, meaning cybercriminal activity such as darknet market sales or ransomware attacks in which profits are virtually always derived in cryptocurrency rather than fiat currency.
It’s more difficult to measure how much fiat currency derived from offline crime — traditional drug trafficking, for example — is converted into cryptocurrency to be laundered. However, we know anecdotally this is happening, and later in this section provide a case study showing an example of it.
Overall, cybercriminals have laundered over $33 billion worth of cryptocurrency since 2017, with most of the total over time moving to centralized exchanges. For comparison, the UN Office of Drugs and Crime estimates that between $800 billion and $2 trillion of fiat currency is laundered each year — as much as 5% of global GDP. For comparison, money laundering accounted for just 0.05% of all cryptocurrency transaction volume in 2021. We cite those numbers not to try and minimize cryptocurrency’s crime-related issues, but rather to point out that money laundering is a plague on virtually all forms of economic value transfer, and to help law enforcement and compliance professionals be aware of just how much money laundering activity could theoretically move to cryptocurrency as adoption of the technology increases.
The biggest difference between fiat and cryptocurrency-based money laundering is that, due to the inherent transparency of blockchains, we can more easily trace how criminals move cryptocurrency between wallets and services in their efforts to convert their funds into cash. What kinds of cryptocurrency services do criminals rely on for this?

For the first time since 2018, centralized exchanges didn’t receive the majority of funds sent by illicit addresses last year, instead taking in just 47%. Where did cybercriminals send funds instead? DeFi protocols make up much of the difference. DeFi protocols received 17% of all funds sent from illicit wallets in 2021, up from 2% the previous year.

That translates to a 1,964% year-over-year increase in total value received by DeFi protocols from illicit addresses, reaching a total of $900 million in 2021. Mining pools, high-risk exchanges, and mixers also saw substantial increases in value received from illicit addresses as well.
We also see patterns in which types of services different types of cybercriminals use to launder cryptocurrency.
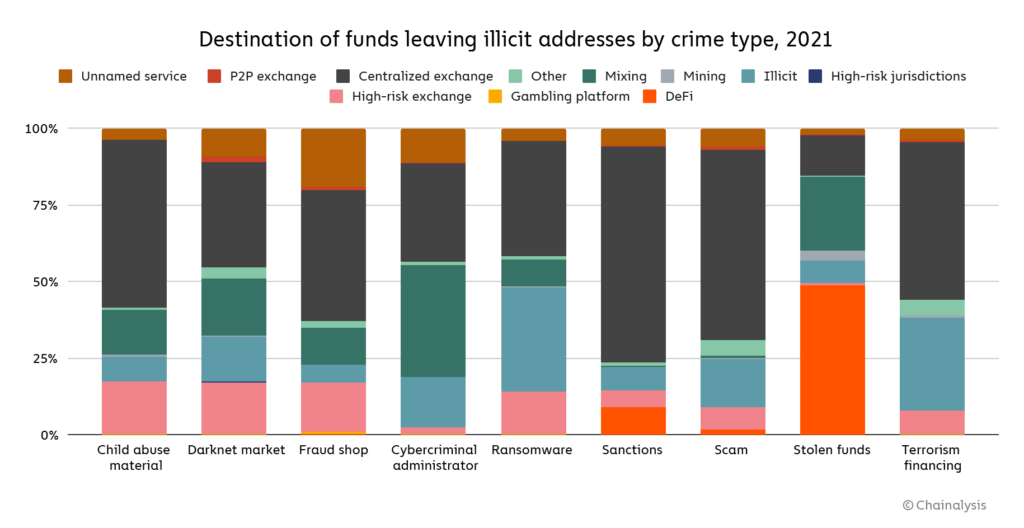
One thing that stands out is the difference in laundering strategies between the two highest-grossing forms of cryptocurrency-based crime in 2021: Theft and scamming.
Addresses associated with theft sent just under half of their stolen funds to DeFi platforms — over $750 million worth of cryptocurrency in total. North Korea-affiliated hackers in particular, who were responsible for $400 million worth of cryptocurrency hacks last year, used DeFi protocols for money laundering quite a bit. This may be related to the fact that more cryptocurrency was stolen from DeFi protocols than any other type of platform last year. We also see a substantial amount of mixer usage in the laundering of stolen funds.
Scammers, on the other hand, send the majority of their funds to addresses at centralized exchanges. This may reflect scammers’ relative lack of sophistication. Hacking cryptocurrency platforms to steal funds takes more technical expertise than carrying out most scams we observe, so it makes sense that those cybercriminals would employ a more advanced money laundering strategy.
More details here: DeFi Takes on Bigger Role in Money Laundering But Small Group of Centralized Services Still Dominate
Dariusz Mazurkiewicz – CEO at BLIK Polish Payment Standard
Banking 4.0 – „how was the experience for you”
„To be honest I think that Sinaia, your conference, is much better then Davos.”
Many more interesting quotes in the video below: