Recorded Future released its 2025 Identity Threat Landscape Report. „Credential theft is the dominant initial access vector for enterprise breaches”.
Recorded Future has released its 2025 Identity Threat Landscape Report, highlighting credential theft as “the dominant initial access vector for enterprise breaches.” It’s not just that lots of credentials are being stolen: the rate of theft is a sharp upward curve. Recorded Future identified 50 percent more credentials in the second half of 2025 than in the first half of the year, and 90 percent more credentials in the last three months of the year than in the first three months.
Executive summary
In 2025, Recorded Future detected:
. 1.95 billion malware combo list credential exposures
. 36 million database combo list credential exposures
. 24 million database dump credential exposures
. 892 million malware log credential exposures
Five findings stand out from the data:
- Credential theft accelerated as the year progressed. Recorded Future identified 50% more credentials in the second half of 2025 than in the first half of the year. 90% more credentials were identified in the last three months of the year than in the first three months
- Stolen credentials are targeted, not random. Of the 7 million credentials indexed with identifiable authorization URLs, 63.2% were tied to authentication systems. VPNs, RMM tools, cloud platforms, and detection software also featured prominently — meaning attackers are often going directly for the systems that provide the broadest access and, in some cases, the ability to blind security teams entirely.
- Infostealer malware is outpacing traditional breach detection. Each compromised device yielded an average of 87 stolen credentials. The scale and precision of modern infostealers means a single infected endpoint — including a personal device used to access corporate systems — can expose an entire organization.
- MFA alone is no longer sufficient protection. 276 million of the credentials indexed in 2025 included active session cookies, meaning attackers can bypass multi-factor authentication entirely. This represents 31% of all malware-sourced credentials.
- Detection speed is the decisive advantage. Over half of all credentials (53%) were indexed within one week of exfiltration, and 36.4% within 24 hours. Organizations that act on intelligence quickly can intervene before stolen credentials are exploited.
The Scale of the Problem: Compromised Credentials in 2025
Volume Grew Throughout the Year
Credential compromise from malware logs was not a static risk in 2025 — it compounded. Recorded Future observed a consistent upward trend throughout the year, with the second half producing 50% more indexed credentials than the first.
The final three months of the year were particularly active: They saw 90% more volume than the first three months, reflecting both the continued proliferation of infostealer malware-as-a-service (MaaS) and the disruption and reformation of major malware families mid-year (covered in detail in the malware section below).
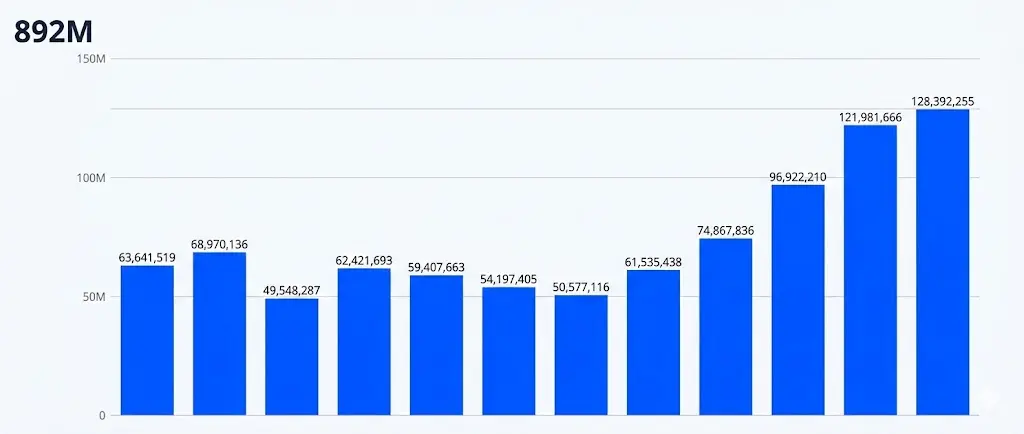
CHART 1: Monthly credential volume from malware logs, full year 2025 (Source: Recorded Future)
What this means for security teams: Seasonal or quarterly threat reviews are insufficient. The volume and pace of credential exposure in 2025 demands continuous monitoring — not periodic audits.
What do Those Credentials Actually Unlock?
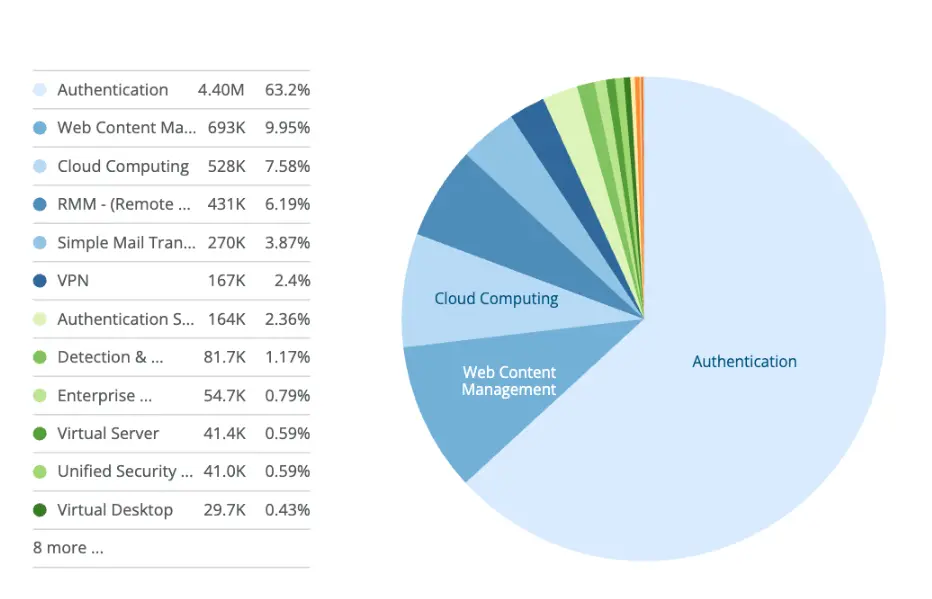
CHART 2: Top authorization URL categories, 2025 (Source: Recorded Future)
More credentials exposed means more doors open to attackers. The authorization URL data from 2025 reveals exactly which doors they’re targeting — and the picture is stark.
Of the 7 million credentials with high-risk authorization URLs indexed in 2025, 63.2% were tied to authentication systems. The next largest categories were web content management (9.95%) and cloud computing (7.58%), followed by remote monitoring and management tools (6.19%) and email infrastructure (3.87%).
This is not a random distribution. Authentication systems, cloud platforms, and remote access tools — VPNs at 2.4% and RMM tools at 6.19% — are precisely the systems that give attackers the broadest foothold inside an organization. A single stolen credential for an authentication portal or VPN can serve as the entry point for lateral movement, privilege escalation, and ultimately a full breach.
The presence of detection and response software (1.17%) and SIEM platforms (0.06%) in this list is particularly notable. Credentials for the tools organizations rely on to detect attacks are themselves being stolen — giving attackers the ability to blind security teams before they strike.
What this means for security teams: The value of a stolen credential is determined by what it unlocks. Prioritize monitoring and rapid response for credentials tied to authentication systems, remote access tools, cloud infrastructure, and security platforms — these can represent the highest-leverage targets for attackers operating with stolen credentials.
Recommendations for Security Teams
The 2025 data points to four areas where security teams can meaningfully reduce their exposure to credential-based attacks.
1. Extend monitoring to personal devices. The majority of infostealer infections occur on personal devices used to access corporate systems — a risk that endpoint detection tools and traditional perimeter controls cannot address. Monitoring infostealer malware logs directly provides visibility into these exposures before they are weaponized.
One large automotive parts distributor found that Recorded Future surfaced stolen credentials tied to an employee’s personal device — an exposure their existing tools had no visibility into and would likely never have caught.
2. Treat session cookie exposure as a critical-severity event. With 276 million credentials carrying active cookies in 2025, any infostealer-sourced credential exposure should trigger immediate session invalidation in addition to a password reset. MFA bypass via stolen cookies is not a theoretical threat — it is an observed, frequent attack pattern.
3. Automate response workflows to close the detection-to-remediation gap. The data shows that most credentials are indexed within days of theft. Organizations that have pre-built response playbooks — automatically checking Active Directory, clearing sessions, forcing resets, and notifying managers — respond in minutes rather than hours.
„We created a custom SOAR playbook using the Identity Intelligence module. This playbook takes the information of compromised corporate user accounts, runs an Active Directory check for the credentials, clears user sessions and resets the password if the account is found to be compromised. It also notifies the user’s manager for email response. To date, we have processed over 330 different identity alerts. ” – said Bryan Cassidy, Lead Cyber Defense Engineer, 7-Eleven.
4. Monitor your entire domain footprint — including subsidiaries and third parties. Some of the most consequential exposures in 2025 involved obscure subsidiaries and supply chain partners, not core corporate domains. Attackers do not limit themselves to obvious targets. Security teams shouldn’t limit their monitoring to obvious domains either.
One large international financial services firm detected an infostealer on a third-party service provider’s machine through Recorded Future — surfacing a supply chain exposure that would have been invisible through traditional monitoring alone.
Detection Speed is “the decisive advantage”
The gap between when credentials are stolen and when a security team finds out is where breaches happen. Most organizations discover compromised credentials days or weeks after the fact — through a public breach disclosure, a tip from law enforcement, or an incident that’s already underway.
Recorded Future closes that gap. In 2025, 36.4% of all indexed credentials were detected within 24 hours of exfiltration, and 52.9% within one week. By the time stolen credentials are being traded or weaponized, Recorded Future customers have already been alerted.
Speed matters because attackers move fast. Infostealer logs are often listed for sale within hours of collection. Every day between exfiltration and detection is a day an attacker may already have access. The 15.3% of credentials not detected within a month illustrate what happens when that window stays open – extended attacker dwell time, lateral movement, and incidents that escalate into major breaches.
More details here: Inside the Infostealer Economy: Credential Threats in 2025
____________
This report is based on data indexed by Recorded Future’s Identity Intelligence Module across the full calendar year 2025. Recorded Future monitors credentials across open web, dark web, paste sites, Telegram channels, and infostealer malware logs sourced from 30+ malware families. All credential data can be processed and analyzed without storing plaintext passwords in customer-facing systems.
Dariusz Mazurkiewicz – CEO at BLIK Polish Payment Standard
Banking 4.0 – „how was the experience for you”
„To be honest I think that Sinaia, your conference, is much better then Davos.”
Many more interesting quotes in the video below: